Curse You Google Software Updates!
I try to keep track of changes to the software on my machine. I look for programs run out of unusual locations (possibly malware dropped on my machine) and modifications made to existing programs (possibly installing Trojan version of the program). To track which programs were running or being changed I used Apple's BSM audit data.
I quickly realized how naive this simple view was. Today's operating systems and applications are constantly updating themselves. Sometimes they notify you to the change, but more and more frequently they just do it behind the scenes and never tell you about it.
Google may have led the way with this, quietly and frequently updating their software like Google Chrome. I wrote a pair of articles about how this software could serve as a model for malware that an Advanced Persistent Threat (APT) could use to maintain a presence inside your network:
The Advanced Persistent Threat You Have: Google Chrome
The Making of "The Advanced Persistent Threat You Have: Google Chrome"
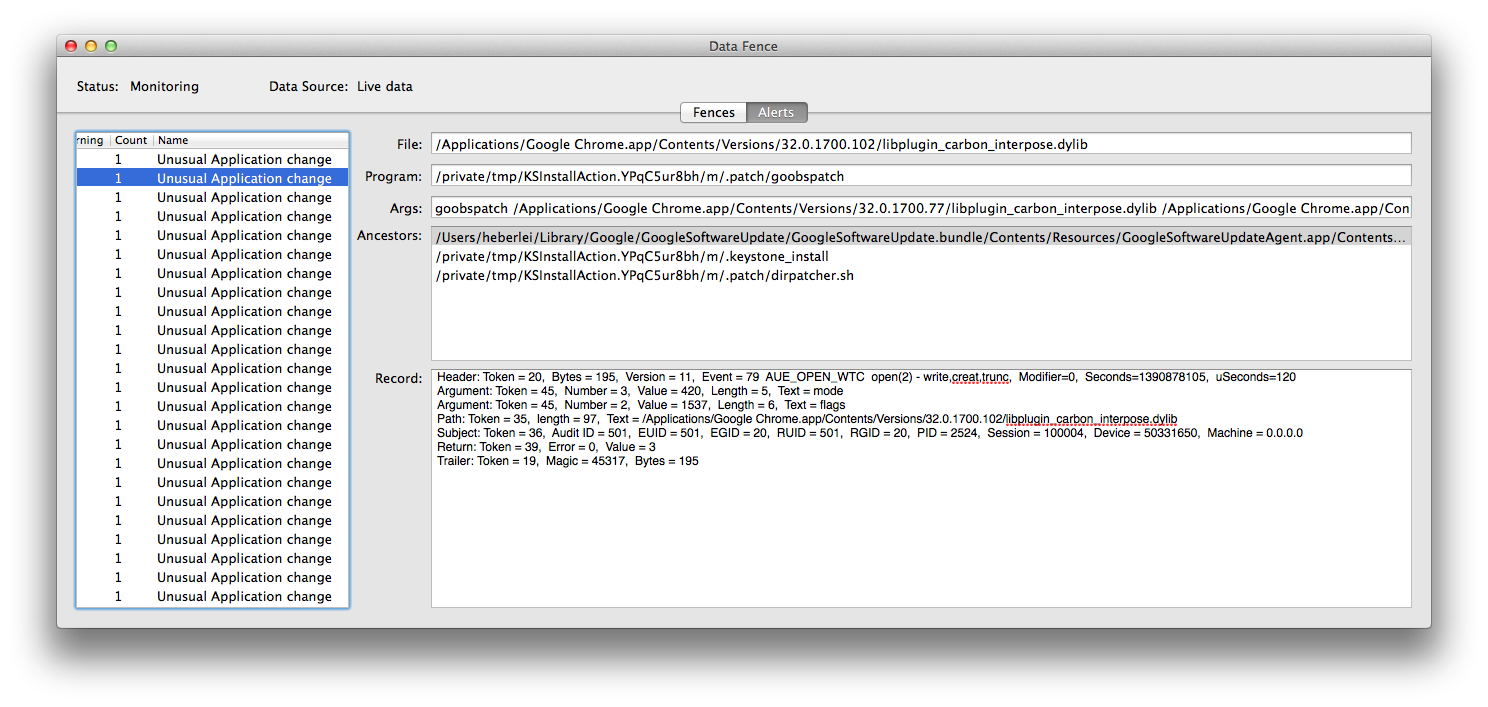
Recently, as I've been developing my Data Fence program, I've had to revisit this problem, and Google has again been annoying me.
I have a fence rule that tracks updates to files in the /Applications folder. Part of that fence rule requires me to specify legitimate pathways that can lead to changes to applications, and now I think I've seen Google Chrome update itself through programs installed in at least three different locations. Arg!
/Users/heberlei/Library/Google/GoogleSoftwareUpdate/GoogleSoftwareUpdate.bundle/Contents/Resources/GoogleSoftwareUpdateAgent.app/Contents/MacOS/GoogleSoftwareUpdateAgent
/Users/heberlei/Library/Google/GoogleSoftwareUpdate/GoogleSoftwareUpdate.bundle/Contents/MacOS/GoogleSoftwareUpdateDaemon
/Library/Google/GoogleSoftwareUpdate/GoogleSoftwareUpdate.bundle/Contents/MacOS/GoogleSoftwareUpdateDaemon
When I get it wrong (last night I only had two of these pathways marked), Data Fence lights up (and in this case it also purrs since Data Fence includes sound effects) while Google Chrome is updating itself. At this stage of testing I actually find this amusing, but I need to address this issue.
Another lesson learned I guess. I've generalized the regular expression for this match a bit more, and I realized I hadn't added the "track current working directory" code back into the audit analysis program. I guess that is today's task.